Cross-chain swap and DEX aggregator platform LI.FI protocol was hacked yesterday, March 20th, for over 200 Ether. The attacker used a weakness in the protocol’s core offering, the swap function, to launch an attack that stole from a contract which doesn’t hold any funds. How is that even possible?
The answer lies in token approvals. As I discussed in Basic Rug Protection, token approvals are poorly understood and very dangerous if misused. First, let’s understand how a DEX works architecturally.
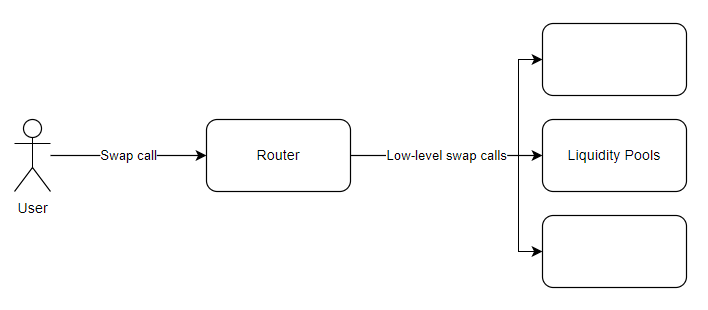
Users interact with a single router contract which will perform one or more low-level swap calls on the relevant liquidity pools.
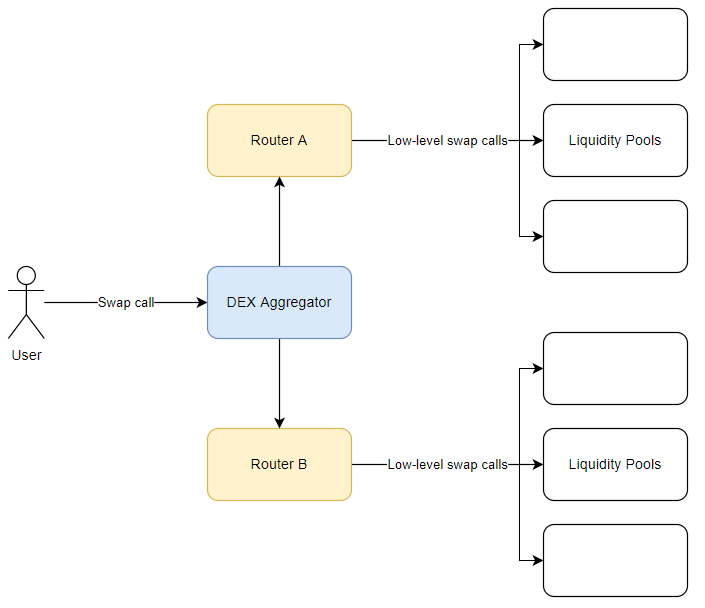
DEX aggregators work in a similar fashion. Swap calls are made to the aggregator router, which then calls one or more DEX routers, which call their low-level swaps on the liquidity pools.
Notably, in both patterns, the initial point of entry (router or aggregator) has to be approved to transfer tokens on the user’s behalf! Contrary to popular understanding, once a contract has token approval, it does not need ANY interaction from the user to spend those tokens like they were its own money. It can move them at any time of its choosing until the user revokes approval.
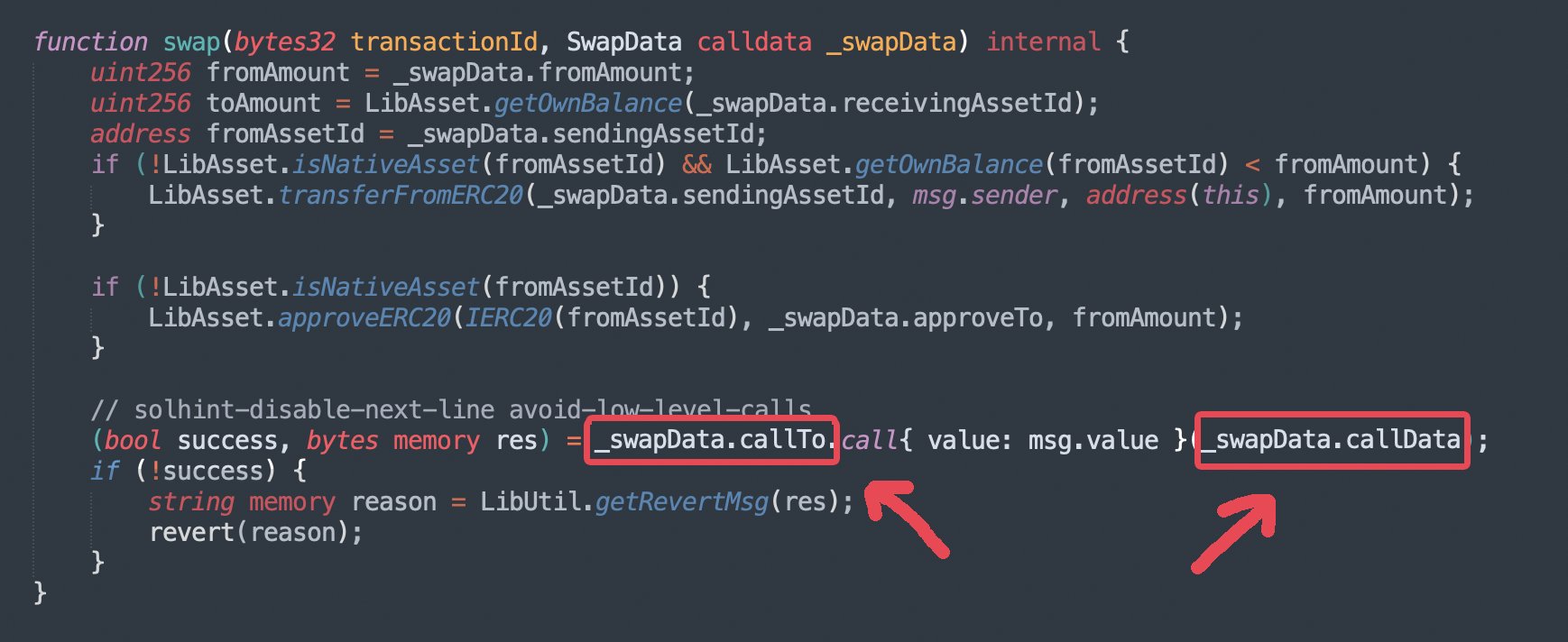
This is the exploit route used by the hacker. The affected router contract did not actually hold any tokens – but it did hold token approvals. Combined with use of a low-level call function in the router that would execute arbitrary, user-provided code, and the exploit was set. The attacker was able to get the swap router to transfer all the tokens it held user approval for to the hacker’s wallet.
The Li.Fi team states that the exploit has been patched by removing the ability to call arbitrary addresses, instead requiring the destination to be one of several approved DEXs. Twenty-five of the affected twenty-nine users have already been compensated by the team, according to their press release in the blog below.