Making secure cross-chain bridges is not easy work, as Axie Infinity’s developers Sky Mavis found out. The leading GameFi protocol runs on the Ronin blockchain, which is optimized for gaming. On March 23rd, the Ethereum side of the Ronin bridge was hacked, for the loss of 173,600 ETH and 25.2 million USDC (~$545 million total at time of exploit, over $620 million when discovered). Miraculously, this cataclysmic exploit went totally unnoticed until 6 days later, on March 29th, when a whale tried to withdraw 5,000 ETH from the bridge and could not.
The Hack
The hack hinged on the bridge validation process. As a reminder, smart contracts can’t see across chains. To move assets safely, the contract on Chain A needs a cryptographically provable way to know that the corresponding deposit on Chain B has been made, before A releases funds. The Ronin bridge used a proof-of-authority scheme, where the only requirement to move funds was 5 out of the 9 validators signing a message for its withdrawal.
This is extremely weak security, especially as rollups come into maturity. 4 out of the 9 validators were controlled by Sky Mavis, the company behind Axie Infinity. The attacker somehow compromised the private keys to these accounts, and the fate of the bridge now rested on one honest signature.
Unfortunately, the Sky Mavis validators had access to another signature. Previously, one of the validators was controlled by Axie DAO. For logistical reasons during times of high chain throughput, that organization gave Sky Mavis the ability to sign messages on its behalf. While that temporary arrangement ran its course, the access was not revoked. The attacker compromised this key as well, giving him the needed 5/9 signatures, and the final infinity stone.
In a snap, the Ethereum side of the bridge was drained.
The Lack
The exploiting transaction happened 6 days ago. No one noticed.
Let’s say that again for effect. Not a single team member noticed that half a billion dollars evaporated, destroying the functionality of a critical piece of infrastructure.
Any serious company would have automated monitoring in place. There are multiple solutions which can do this. CertiK Skynet. OpenZeppelin Defender. Tenderly. These platforms are so easy to use that I could set up an alert on the contract’s balance in 30 seconds. They’re so easy to use I wrote a whole guide on how to monitor smart contracts automatically.
Even if you don’t want to set up automatic monitoring, maybe you would, I don’t know, look at your contracts once in a while?
This is incredible negligence on the part of the Sky Mavis operations team. Jaw-dropping, staggering, incompetence.
The Escape
The attacker is behaving rather erratically by some standards. Rather than the default option of making a sprint for Tornado Cash, the attacker has been distributing Ether to several addresses, and cashing them out to CEXs – FTX, Huboi, and Crypto.com. It was also funded from Binance, in defiance to the typical Tornado Cash pattern.
This suggests either a hacker that was colossally, monumentally stupid in cashing out via KYC exchange – or a savvy hacker washing funds via the CEX.
If the hacker had access to compromised FTX accounts, or set up arrangements offline to move money through the accounts in exchange for a premium, the KYC link would not lead back to the hacker. Given that the original exploit occurred through a private key compromise, and not on-chain means, there is good circumstantial evidence for this.
Maybe a traditional hacker got lucky and stumbled across some keys. Maybe it was a targeted attack on the Sky Mavis infrastructure. The investigation is ongoing, and the Sky Mavis team, still reeling from the attack, has not posted a further post-mortem.
For now, we can only wait.
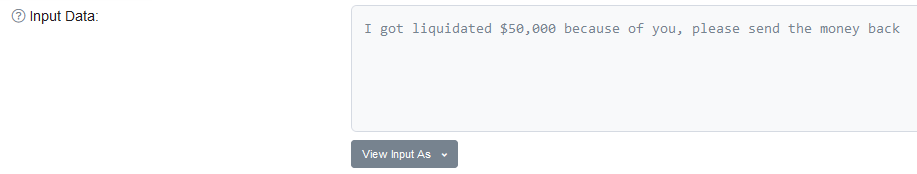
And watch the usual stream of “please sir, mi familia” messages stream in to the exploiter’s account.

I don’t like making these posts – every hack represents someone’s financial future turned upside down. I hope this is the last one I write, but I doubt it will be.